What to do when a vendor is breached.
Welcome to the CXO Nexus monthly InCight Insider newsletter where we provide helpful notes on how to leverage your CIO InCight® data.
Hi InCight Insider,
The Holiday season is in full swing and companies are closing out the year. Unfortunately, cyber bad actors continue their activities with increasingly sophisticated attacks that require constant diligence for what seems an infinite threat landscape. Here are some CIO InCight features to review for your organization in response to cyber threats and breaches. Also included is a webinar snippet with NASDAQ on solving the reseller conundrum with AI technology from CXO Nexus.
How CIO InCight is leveraged when a vendor is breached.
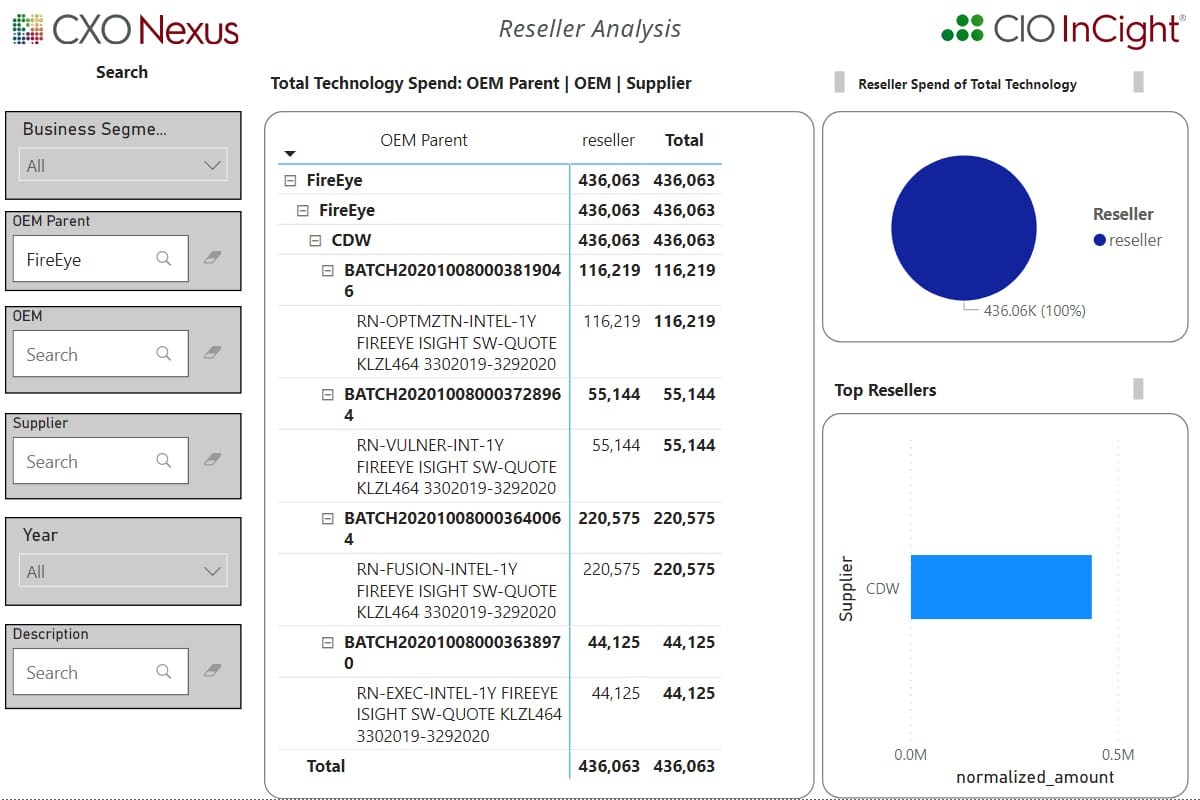
When a high profile cyber breach like FireEye is breaking news, being able to quickly identify spend with a breached third party is critical to prepare your response. It’s difficult to know your exposure if you can’t identify spend with a breached supplier - especially when the products are purchased through a reseller.
CIO InCight provides companies the ability to identify OEMs, Software Publishers and Service Providers purchased through resellers by querying their AI & ML based Augmented Data.
Below is an example of FireEye products purchased through a reseller, derived from querying the Augmented Data, created by the CIO InCight AI & ML engine. Accounts payable systems and/or basic category spend reporting is not going to get this type of visibility – that is why clients make CIO InCight their go to source for vendor spend.
Use Case:
NASDAQ discusses how CIO InCight provides
previously unavailable reseller spend by manufacturer.
Have questions?
We have more year-end tips to share. Your feedback is welcome on the InCight Insider at support@cxonexus.com.
Visit CIO InCight at: https://app.cxonexus.com/#/signin.
If you have issues signing in contact us at support@cxonexus.com.
Best,
Leif
 Leif Easterson
Leif Easterson
Global Head Customer Success
LEasterson@cxonexus.com

Transforming Data to InCight®

Customer challenges and insights gained by using CIO InCight.
Each one is a chapter in discovery, finding hidden details of the vendor spend data ingested. Our ML & AI-driven Intelligent Fusion Engine IFE® is used to clean and normalize down to the item level and will reveal actionable information.